Commercial USB Keyloggers
USB keyloggers can only be used with USB keyboards, while Lumberjack can be used with any keyboard, including a laptop. Furthermore, an accelerometer pad hidden under a laptop is more subtle and less likely to be detected by an uninformed user, compared to a USB-connected device. Finally, many keyloggers simply store the keystrokes to the device itself, and the device must be physically retrieved. Lumberjack will feature streaming of the keystrokes, utilizing Wi-Fi and a virtual file system to enable remote access of the keystroke data. Thus, Lumberjack will never need to be physically retrieved and will allow the keystrokes to be viewed in near-real time.
Acoustic Data Based Keyloggers
Much research has been conducted on keyloggers that utilize acoustic data, using the differing tones of keystrokes to classify which key is being pressed. Unlike acoustic keyloggers, our product could be used in a variety of settings, including commonly noisy ones. Accelerometer data is prone to less outside interference, and its accuracy should have little variance based on location.
Phone Gyroscope Based Keyloggers
In 2011, researchers at Georgia Tech published preliminary research showing how a hijacked phone sitting near a keyboard could pick up distinct keystrokes using the phone's accelerometer. The researchers were able to get an impressive 80% accuracy just by using an iPhone several inches away. Lumberjack's data will come from directly beneath the keyboard rather than from a nearby phone and thus will have better accuracy of detected keystrokes. Plus, by bypassing the need for a phone, an attacker or pentester need not create a rootkit for the phone of their target. One only needs physical access once in order to begin collecting accurate keystroke data.
Architecture
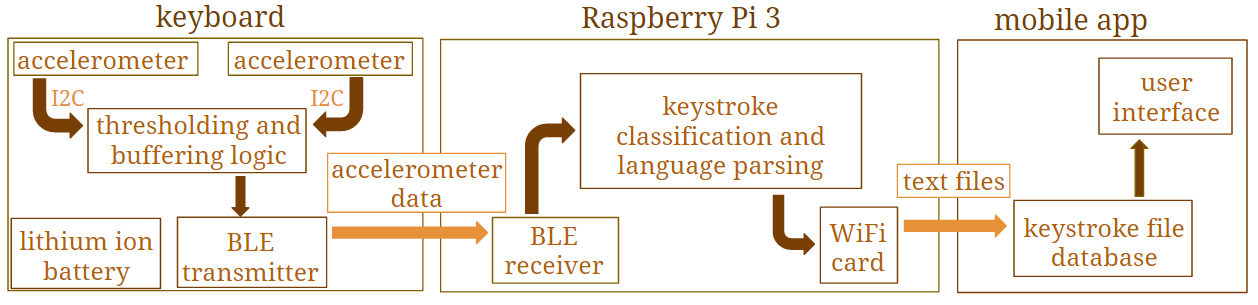
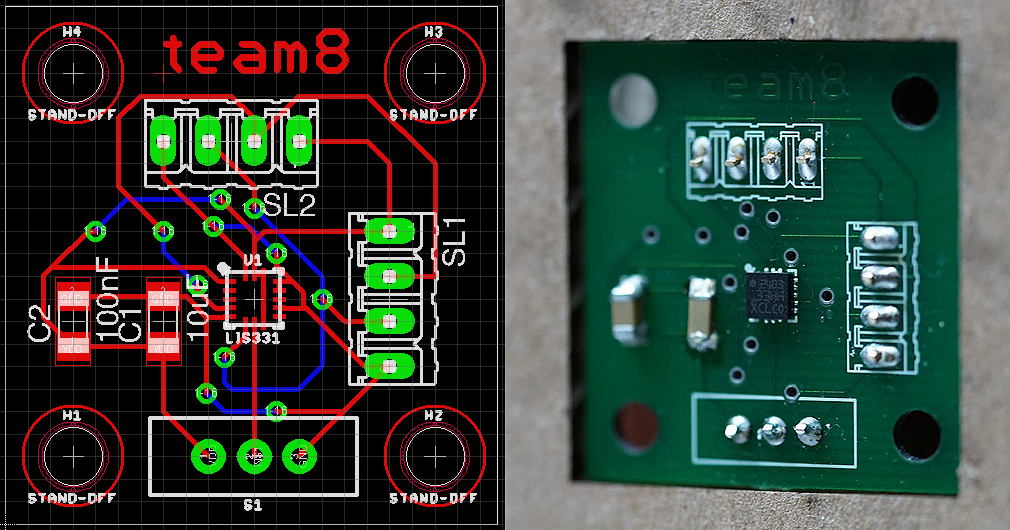
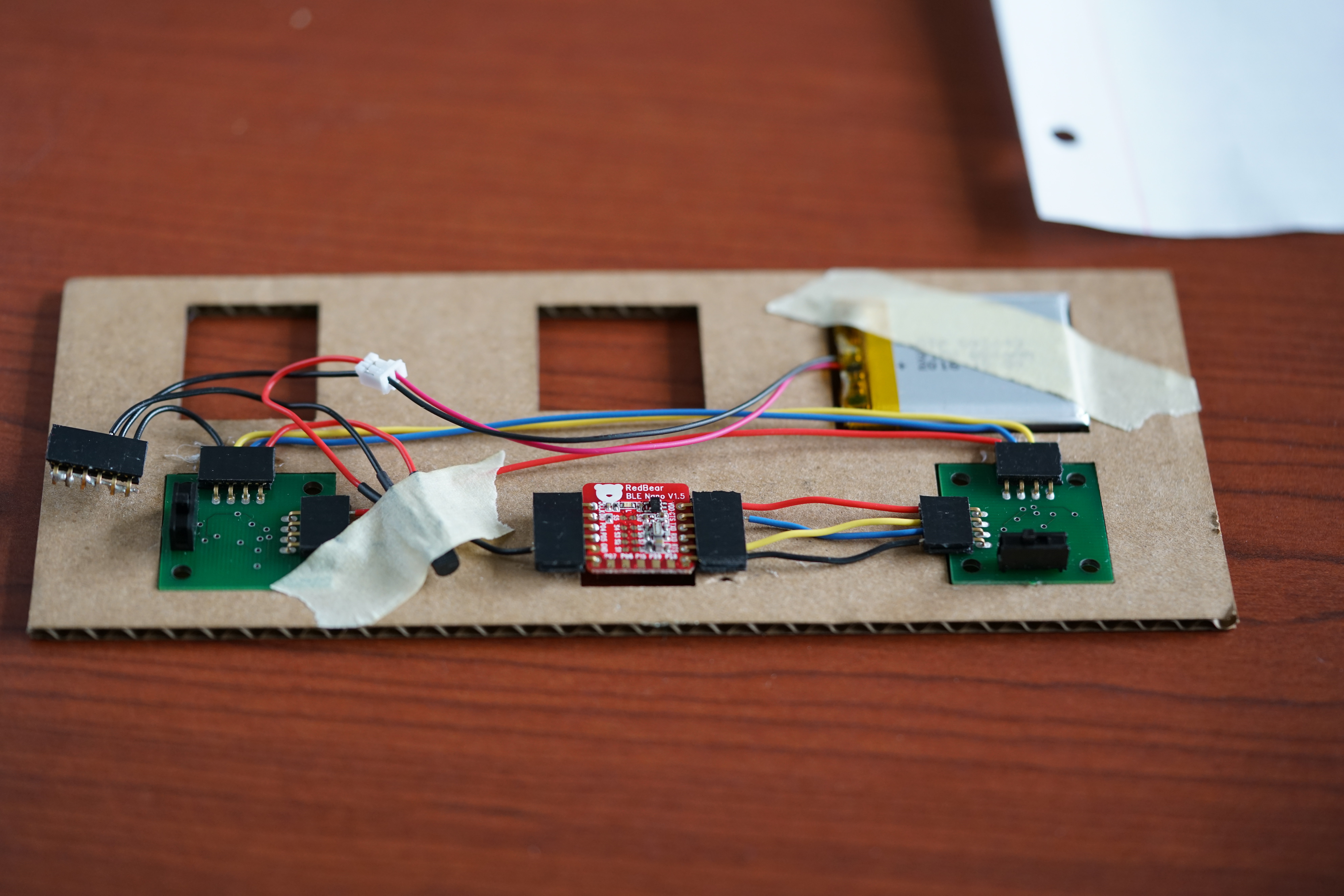
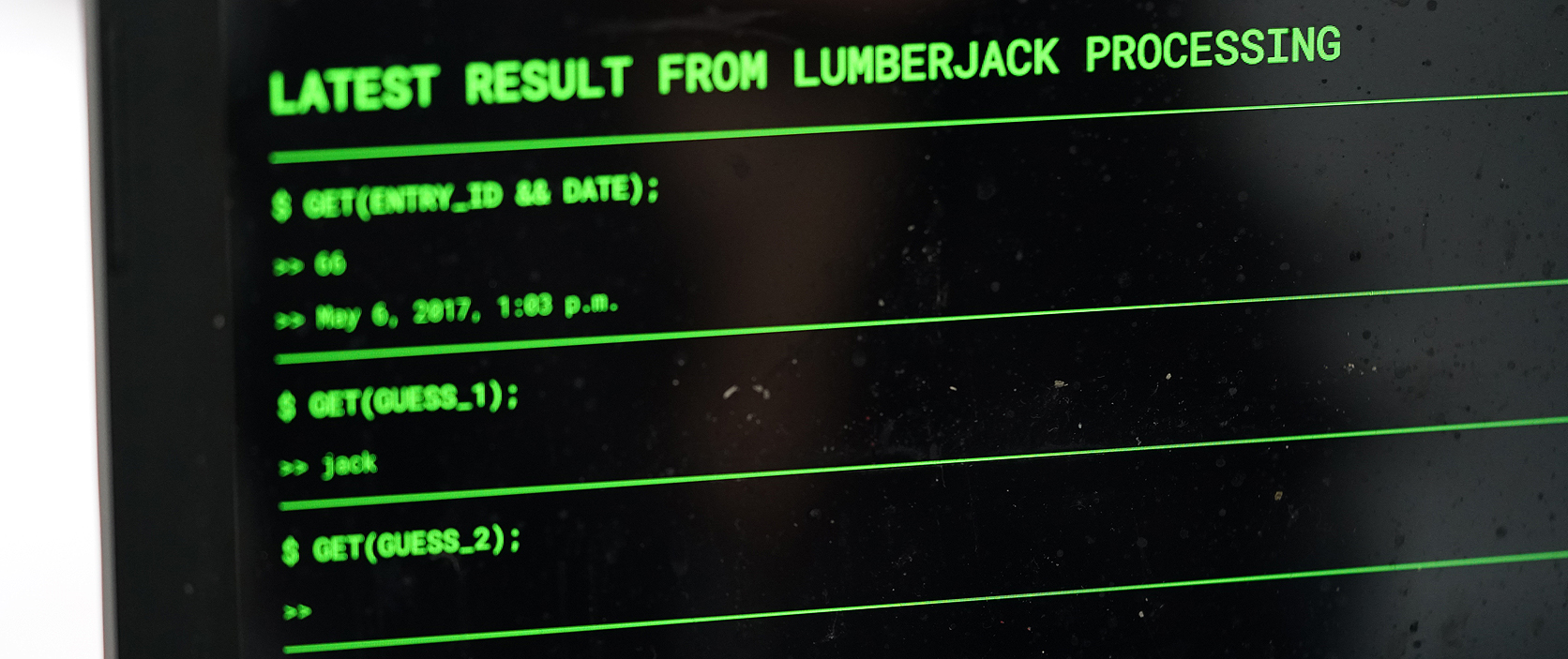
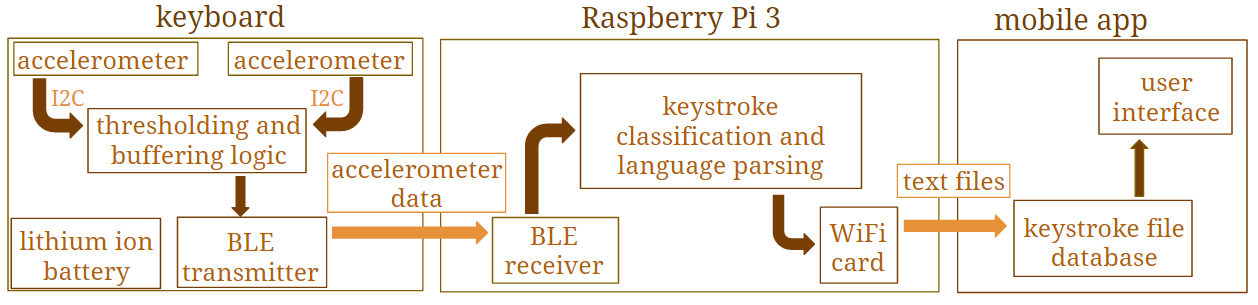
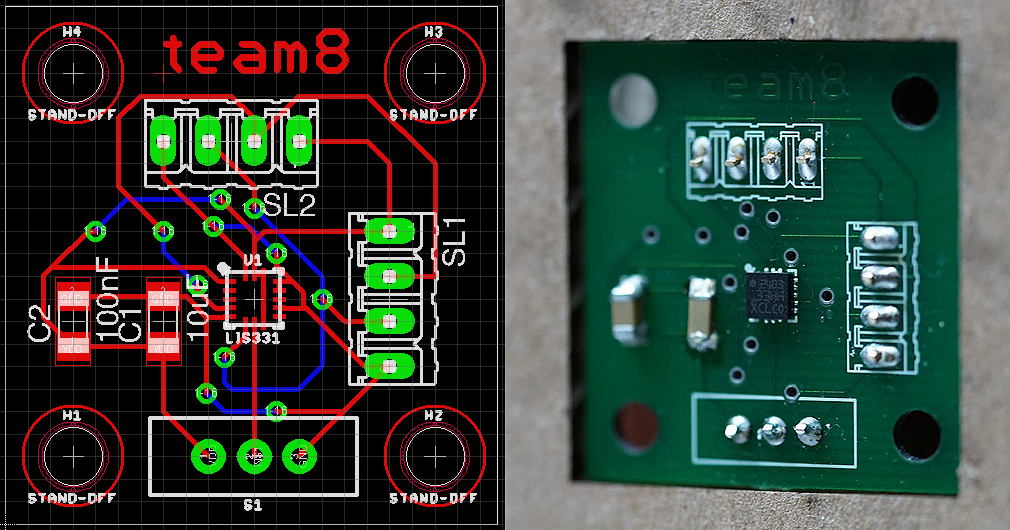
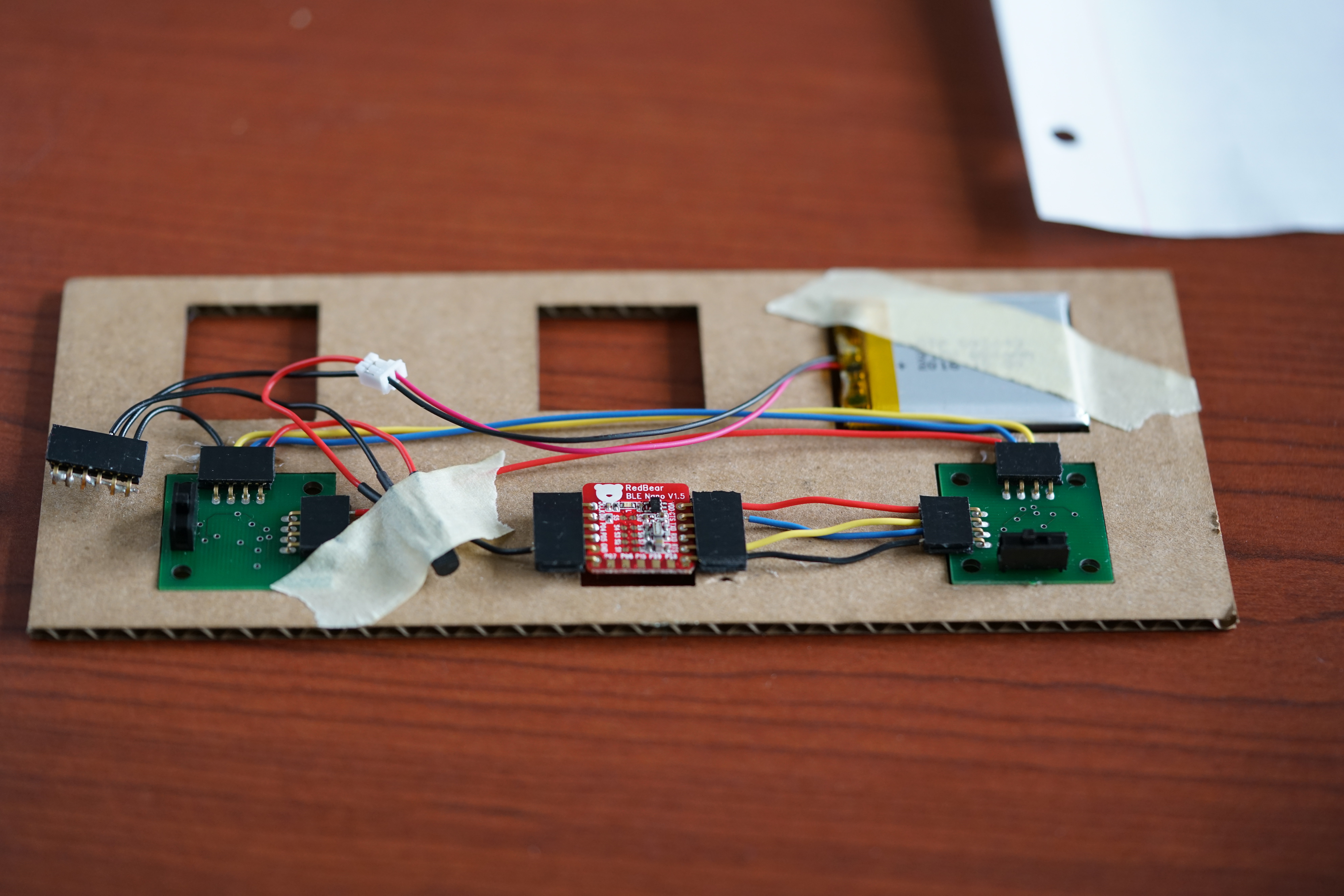
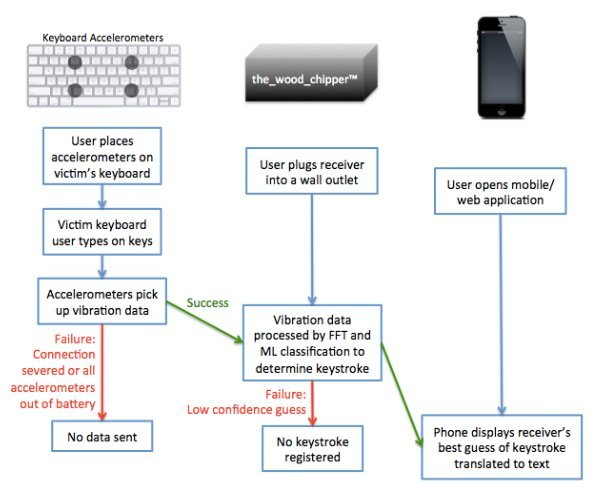
Our system consists of 3 functional components: the under-keyboard data collection components, the receiver and processing box, and the remote database. Two acceleration sensors and a BLE peripheral module will be placed in a cardboard chassis that can be secured underneath a victim's keyboard. These three components are powered by a single lithium-ion battery, as each of these components is intended to be low power and discreet. For the acceleration sensors, we created our own breakout boards for each of our two accelerometers, in order to easily spread them out underneath the keyboard. These boards are wired directly to the RedBear BLE Nano module for communication over I2C, where we will determine whether the the accelerometer data is significant; that is, the BLE Nano will only send data that it belives to be part of a keystroke. This is accomplished by using a pre-set threshold for the accelerometers' Z-axis data: if a sample's Z-axis data is significantly higher or lower than this threshold, then we queue this data sample to be sent. The BLE Nano will send its data using the Bluetooth Low-Energy protocol to our processing box, implemented by a RaspberryPi 3. The Pi will receive the accelerometer data and run a classification program that attempts to match the three-axis values with discernable keystrokes. We use a support vector machine to classify data based on whether the keystroke occurred on the left or right of the keyboard, as well as whether the keystroke occurred in the top, middle, or bottom rows. Once the Pi has classify each keystroke it received, it can coalesce these keystrokes into words that it guesses from a supplied dictionary. This dictionary can be swapped out to support different contexts and languages, since our algorithm classifies over keystrokes. Finally, the Pi will send its top 5 guess as to what words were typed, and it will send its guesses over WiFi to a database, located on a remote server. Users will be able to retrieve this data using a web interface, which can be found here.
Below are our PCB design for one accelerometer and photos of our finished PCBs and full under-keyboard rig.